Active Sniffing Attacks
Mac-Attacks:
MAC-flooding is an attack where the CAM table is flooded with fake MAC-IP pairs, so CAM table overflows causing traffic to flood all ports on switch (i.e) changing switch to behave like a hub
ARP Spoofing:
In this case, an attacker can spoof the MAC address of a trusted host and forge ARP request/replies to overload the Switch. Then the switch is set in “forward mode” an attacker can now sniff the packets on the traffic.
ARP Poisoning:
Attacker chooses targets and floods their ARP cache with forged entries thus replacing the MAC address of targets with MAC address of attacker. ARP poisoning is used in Man in the middle attack.
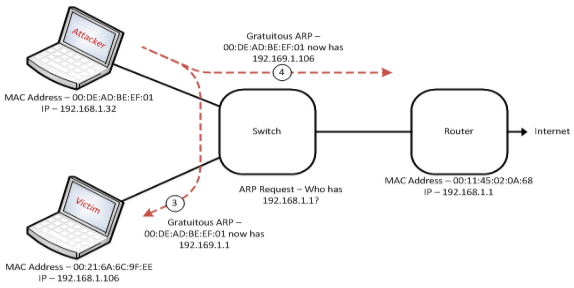
Source:http://www.shortestpathfirst.net/2010/11/18/man-in-the-middle-mitm-attacks-explained-arp-poisoining/
Man-in-the-middle Attack:
It’s a targeted attack, where attacker sniffs the traffic and chooses targets. It uses ARP poisoning method to forge fake ARP request/reply to targets forcing them to update their ARP cache with MAC address of Attacker machine in the place of the genuine target. So the traffic between target’s will be split into two. One connection between target1 and attacker and other between target2 and attacker. So the attacker being the man in the middle can modify/replay the traffic. He will be able to capture sensitive information between the targets.
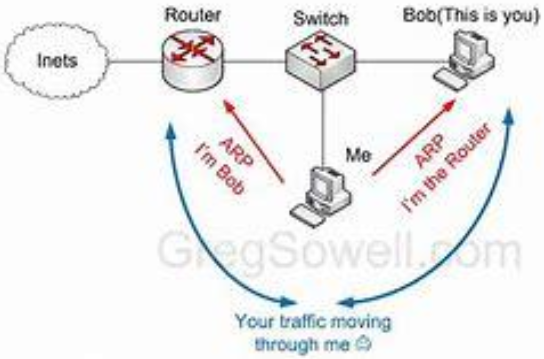
Source: www.gregsowell.com