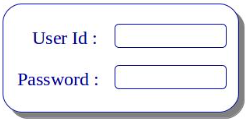
SQL injection is an attack where the hacker makes use of unvalidated user input to enter arbitrary data or SQL commands; malicious queries are constructed and when executed by the backend database it results in unwanted results. The attacker should have the knowledge of background database and he must make use of different strings to construct malicious queries to post them to the target. For Example, in user login screen, username and password are the dynamic fields where users enter the data. Depending upon the user’s inputs dynamic queries will be constructed; the usual query will be Select * from users table where username=’Username.txt’ and password=’Password.txt’. If the input fields are not sanitized properly, then the malicious user can enter some data like this Username = blah’ or 1=1— Password = password Here both username and password are incorrect. But the query which is constructed will be Select * from users where username=’blah’ or 1=1—and password=’password’ The query will run and the user will be granted access. This is because the first part of the query is Select * from users where username=’blah’ or 1=1— Because – is a comment line in SQL, everything following that will be ignored. The query will only validate between username=’blah’ or 1=1. Because 1=1 is always true, the user will be granted access.
Introduction to SQL Injection