Personal Security: How to Eliminate the Internet's Info on You
Sun Microsystems' chief executive officer Scott McNealy famously said in January 1999, “You have zero privacy anyway. Get over it.”
At the time, many people were shocked and outraged over Scott McNealy's remarks. But as the CEO of a powerful computer company like Sun Microsystems, McNealy was simply setting the level of expectations.
Setting the level of expectations for your own personal security and privacy is all about educating yourself to understand the buzzwords.
Let us start with the trail of data you create while using the Internet a.k.a the "digital footprint." Managing your digital footprint requires an understanding of information collected both locally on your browser, as well as on the cloud at individual web sites globally.
Understanding cookies
This is a common form of digital footprint information left behind by you on the web browser while navigating the internet. Let me give an example.
Have you ever used a website and created a shopping cart to buy something, but quit browsing before you placed the order? When you come back to that same site a day later you still see the items you placed in the shopping cart the day before. Why? Cookies. They're little bits of code that store your prior activities. Cookies can also be used to remember arbitrary pieces of information that the user previously entered into form fields.
Knowing that cookies are the most common form of a digital footprint you might be quick to say, "so why not just turn off cookies when using a web browser?" Unfortunately, completely turning off cookies is not always a good idea.

Let's look at an old school analogy to understand how cookies are a necessary part of online shopping. When you walk into an old corner diner you may be greeted by a waitress who takes your order by writing your request down using a pencil and a paper guest check notepad. That paper guest check is carried back to the kitchen where the cook prepares your meal. You receive that paper guest checks to take to the cash register in order to pay for your meal before you leave the diner. In this analogy, the paper guest check illustrates the role of cookies in an online transaction.
Let's go back to our corner diner analogy. Let's say the waitress doesn't know your name - you're anonymous to her. But she keeps track of your order slips. She knows you like apple pie and coffee, she knows you always come in for lunch on Tuesdays. She knows you always come in alone. She does not know your name, but by tracking your activity at the diner, she starts to develop a profile about who you are.
Getting the picture? While the cookies themselves might be totally anonymous information, when collected over a period of time they allow someone to develop a profile about you.
In your web browser, you can enable or disable cookies completely. This is so that they are always accepted or always blocked.
With the assumption that the setting to always accept or always block cookies may not be the best answer, explore the settings in your web browser to view and selectively delete cookies.
Be aware of what data is being left behind when you use a web browser, especially when sharing a computer, or using an office computer that you do not totally control. Learn where the settings are to fully wipe all private data, including cookies, from the computer you are using.
What about browser extensions to secure your browsing?
There are different types of software that offer you safe surfing. Browser extensions are designed to work within a web browser to increase your safety.
One concern with adding things into your web browser is what impact does it have on your browser working properly. Browser extensions may solve a few issues, as well as add a few new ones. One of the first troubleshooting tips when having browsing problems is to disable browser extensions to see if the issues go away.
Another problem with browser extensions is that they often can be the target of malware.
Technology is always changing. We would recommend understanding the settings already built into your browser and experimenting with finding the best settings for your needs before exploring browser extensions.
Safety with social media
The buzzword of the twenty-first century is cloud computing (here's some resource to help you navigate through the types of cloud services). Since the first days of the internet, we have had cloud computing, that simply means the data is kept on remote servers. It's just another way of saying the data is not on your computer - it's on someone else's computer.

When your computer is sitting in your home and is powered off - all your data is still there, residing in your hard drive. If your home is locked, and I can't get to your computer, your data is safe. Correct?
But what about all that information that is on the cloud (also consider checking this perfect guide for cloud computing certification), such as the servers of social media platforms on which your profile exists. Surely, your data is safe there. Correct?
Well, let's take a step back and define safe. If I typed your name into a search engine, what would I learn about you? Would I learn where you live or where you work? What else would I learn?
Let's go back to our example of the corner diner and tracking cookies in your browser. In that example the information being tracked was kept at the diner, representing the business you are visiting.
But now you are posting to social media every time you visit that diner, telling your friends when you stopped there, what you had. Maybe your friends are learning new things about you, and they do know your name. Maybe your information is being shared by a friend of friends, people you don't even know.
Just like with the tracking cookies at the diner, people you don't even know are collecting information about you over a period of time, and are developing a profile about you.
How often do you take inventory of your digital footprint?
Some people might say searching for your name on the internet is showing your vanity. Not entirely. It is researching your digital footprint.
Take a few minutes to look at the privacy settings to see what is shared and how it is shared within each type of social media you use. Every form of social media has some set of privacy settings where you can control the level of access. That said, don't trust any social media outlet to protect your privacy.
If you are having second thoughts about using a social media account, read the terms and services agreement carefully on not only how to close your account, but to have your content removed entirely.
How do I remove every trace of my existence from the internet?
The simple truth is, it is very unlikely you can remove every trace of your existence from the internet.
There are people selling services that claim you can remove every trace of your existence from the internet. I will not say that it is impossible if you have enough time and money, almost anything is possible. But there are some basic flaws in the claims to remove your digital footprint from the internet.
I create a lot of internet content myself, so most of what comes up on search engines with my name on it is content I have created and control. If someone writes something nasty about me, and I do not control the page. I can only hope to write more that is attached to my name, and push down the nasty stuff in the search engine results. If you have something on a page that I created, yes I can delete that page, and eventually, the search engines will stop tracking it. But there are still places I can find that page.
Content Scraping
There is a practice called content scraping where people take content from your site and post it on their own web site. I've written a lot of things on the internet over the past twenty years. Some of the advice and inspiration I share is from my own personal experience.
I have found pages or content that I have created duplicated and hosted all over the internet. I once wrote a poem and used photos of my kids. I found the poem and my kid's pictures on someone else's website. It did not reference me or give any credit to me. Fortunately, I was able to get the content removed.
There is a website called The Internet Archive where you can enter a web address, and it will show you how it looked in the past. They don't archive every site, every day, but they do periodically make copies of sites to archive them. I can find copies of some of my websites there dating back to 1999!
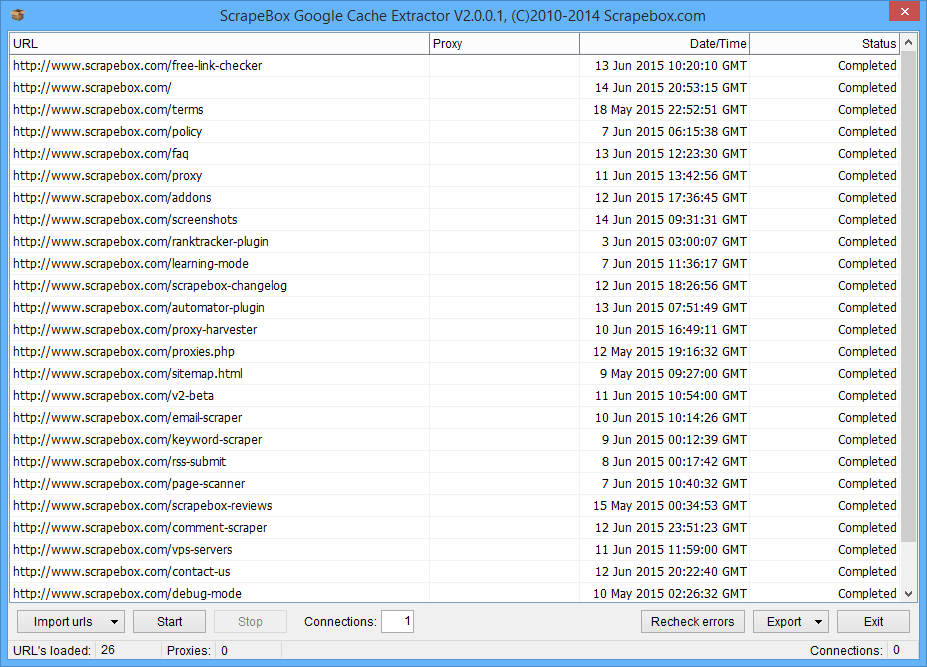
A cache extractor from Google
To elaborate a bit more on the concept of archiving and cache; even if you could entirely delete any memory of your blog from Google, that does not mean that content is gone and can't be found.
Just like people make copies of music and movies - in case they lose the originals - backups of websites are made every day too. Just as I have explained here with scraping and archiving, people make entire copies of websites all the time. Various types of servers cache websites for offline viewing as part of their routine services.
So there is a very important lesson to be learned. There really is no "do-over" button. Think before you post!
Make the most of this lockdown. Become a certified cybersecurity professional now.